Date aired: Nov 30, 2016
Sucuri Remediation Team Lead, Ben Martin, teaches you the key indicators to look for when your Joomla! site has been compromised, and steps needed to clean your site. Ben provides a guide that is helpful if your website has been hacked so you can recovery quickly.
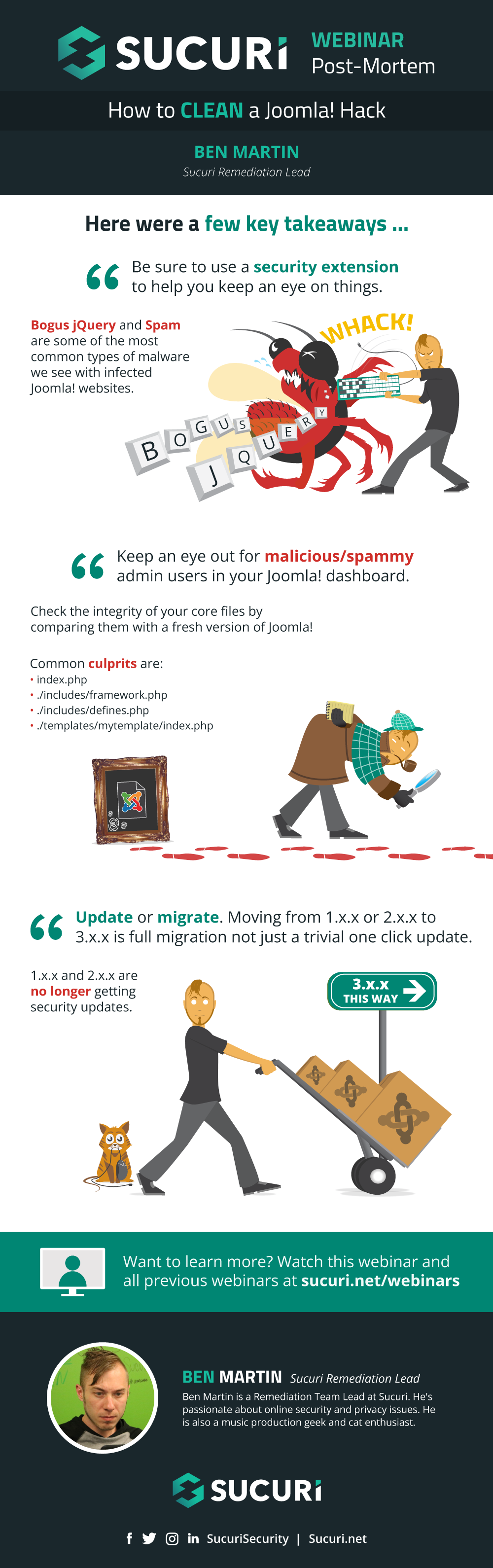

Ben Martin
Remediation Team Lead
Ben Martin is a Remediation Team Lead at Sucuri. He’s passionate about online security and privacy issues. He is also a music production geek and cat enthusiast.
Question #1: You were talking about old joomla sites. How to make it safe witout upgrading?
Answer: The best way would be to put your website behind a web application firewall like CloudProxy. I’m afraid that other than that there is no way to safely use out of date/vulnerable software.
Question #2: How can you install a backdoor at first?
Answer: There are a few ways in which that can be done. If you are using vulnerable software which allows for files to be uploaded to the server that can be the point of entry. If any of your admin credentials are compromised (FTP, administrator, etc) that can also be the source of the backdoor.
Question #3: Suggestion of best extension or service for offsite backup for Joomla 3.x? Files + db. (a client lost their 2.x site due to hard drive failure, currently rebuilding and needs to implement backup)?
Answer: If the server is using cPanel then backups can be made there, otherwise I would recommend that you check out our Sucuri backup service which will take care of automated, daily backups of both files and database and store everything off of your production server.
Question #4: Is RS-Firewall (Joomla Component) recommended? Have you used it before?
Answer: I’ve not used it myself so I can’t say for certain, but I checked out the extension and it seems to have some good features there. However, it should be mentioned that extensions can’t fully protect a website from attacks. A true firewall service will sit between your website and all traffic coming to it and block any malicious traffic from hitting your server. An extension can only deal with malicious traffic once it has already hit your website and also can’t fully protect against DDoS attacks.
Question #5: What did he use to see the difference between the example.com files and the Joomla fresh download files?
Answer: I used the diff command in the BASH command line which is available on both Linux and Mac. If you are using a Windows machine it would be best to use the diff command directly on your server via an SSH connection. You’ll just need to grab a fresh Joomla install and place it next to the website files on your server.
Question #6: Could you recommend some other tools for diffing files and searching for backdoors?
Answer: I’d suggest checking out OSSEC HIDS for checking for such security issues. If you’re not able to install that then I would recommend using SSH/BASH on your server to check for some of the PHP functions that I mentioned during the webinar (ie: base64, eval, preg_replace) by using the grep command to check file contents. Some Joomla security extensions will also auto-scan your website files for suspicious extensions, but don’t trust them 100% because attackers are always writing new code to evade detection and security software needs to have current, updated signatures to find all the new malicious code.
Question #7: If I have been infected with just replace all the files and the database can I clean it? How could I prevent them from re-hacking or updating would be enough?
Answer: Replacing all of your website files with clean copies is a good start, but keep in mind that sometimes attackers will place files that don’t belong on the server that are 100% malicious and just replacing your Joomla core and template/extension files won’t overwrite those. That’s why it’s important to be using a tool like OSSEC HIDS or our server side scanning service which will alert you to new files placed on the server.
Question #8: Are there any recommendations to code the .htaccess file to prevent backdoor entries (i.e. uploading files to server)?
Answer: .htaccess rules probably will not prevent an attacker from uploading a malicious file, however you can disable PHP execution in image and includes directories in order to prevent the backdoors from being utilized even if they are uploaded to the server.
Question #9: Do you think its worth using a tool to search for encrypted code?
Answer: Anything that makes it easier to find malicious code should be welcome. Keep in mind that one of the reasons why attackers encrypt code in the first place is to evade detection, and there are new varients of malicious code created every day which complicates the process of tracking down exactly where it is. I wouldn’t rely on any tool 100% and would recommend using some of the techniques that I described in my webinar (checking for recently modified files, using diff to compare your files with known clean copies) in conjunction with whatever tool you are using.
Question #10: What is the best way to clean an database from malware?
Answer: You can clean the tables one by one but that can be a really time consuming process. A more efficient way would be to use an SQL query to search/replace code like in this example: https:// wpbeaches.com/find-and-replace-across-whole-wordpress-site/ This is for WordPress of course but you can use the same technique: Just replace wp_posts with jos_content and you should be able to remove tons of spam or malicious iframes/code with one single command.
Question #11: What portion of the hacks lately are targeted vs. crimes of opportunity?
Answer: Opportunistic attacks constitue 99.9999% of all attacks. Targeted attacks on your average Joomla website basically do not exist unless the attackers are going after a specific company. Targeted attacks are usually reserved for fortune 500 companies and financial institutions.
Question #12: Do you have any recommended hosting providers for Joomla? We are looking to migrate our site?
Answer: We have partnerships with quite a few different hosting providers so I’m a bit hesitant to endorse one specifically, however I’ve heard good things from our clients about SiteGround. and their hosting seems to be pretty affordable.
Question #13: If I have ssh access, is there a tool/script I can run on my server to automatically scan my core files by a cronjob and have me notified if a core file was tampered?
Answer: OSSEC HIDS would be a good piece of software to run on your server if you want it to auto- scan and notify you of any issues. Barring that, there are some Joomla security extensions that can help monitor your environment, but I’ve never used them myself so I’m not able to make any official endorsements.
Question #14: As far as Security is concerned, which one is more secure? Joomla, Drupal or WordPress?
Answer: Out of the box all three CMS are considered secure, however the issue with all three is the same: extensions. Every peice of software that you introduce into your environment should be considered a new risk. Many website owners get very careless with regards to this and it leads to a bunch of security issues if all of these extensions and plugins are not kept up to date. The more software you have in your environment the more work it is to keep it all well maintained, so I would recommend that you have as few pieces of software as absolutely necessary.
Question #15: Do you have a step by step protocol or manual in which steps are the most important till the less important?
Answer: It really depends on the kind of infection that your website has. If it’s bogus jquery for instance you won’t even need to bother scanning your database. If it’s a spam infection there’s a good chance that the database is the issue so yo would need to give that priority. Most of the time I would suggest checking core and template files first and then going from there.
See all Questions & Answers
ExpandBen Martin – Remediation Team Lead
Hey everyone, thank you very much for attending the webinar today on how to fix a hacked Joomla website. So my name’s Ben Martin. I’m a remediation team lead at Sucuri and I’ve been working at Sucuri for three years and my job is to fix hacked websites, remove malware, and remove websites from blocklists. So just a little about me before we get started, I’m from Victoria, BC. We got a couple other security employees that live here in beautiful Victoria as well and I’ve worked in IT for a total of six years and after three years of working for Sucuri, I’ve lost count the number of websites that I’ve cleaned.
We’re not platform specific, we don’t just clean Joomla sites, we also do Word Press, Magento, Drew Paul, Microsoft, ASB sites, so you know, if it’s hacked and you’re our client, we’ll figure it out and fix it. But today’s webinar is just going to be about Joomla.
So my job isn’t just to remove malware from websites but it’s also to identify new strings of malware, identify campaigns and trends in the website security landscape and provide our research team with samples so that we can improve our tools. And I’ve also attended a number of different CMS related events. Earlier this month I was at … In Vancouver for the Joomla world conference so if any of you watching were also in attendance at Joomla con, hello again.
So I’ve also broken down the webinar into three sections. The first is to actually identify that your website has been compromised. You would be surprised with the number of people that have no idea that they’re websites were hacked. I’ve seen hacks go undetected for several years without the web master even knowing. The second section is going to be how to actually find an remove the malicious code from your site. And the third section is going to be what to do after a hack because that’s arguably the most important part of all three.
Let’s get started! How can you tell if your website was actually compromised. The most common thing that we see is that your website has been blocklisted by google or other search engines or it’s been blocklisted by anti-virus vendors like Norton or Malware Bites and we maintain our own blocklist also. So if you want to check to see if your website is blocklisted, just mosey on down to virustotal.com, type in your web domain name, and then just press enter and it will go ahead and check your website against a whole bunch of different blocklists. Sometimes websites will be labeled ass suspicious or malicious but if your website is on a blocklist or more than on blocklist, that’s a definite sign that something’s going wrong with your site.
Also it’s important to pay attention to what your visitors are saying to you. They might be using a different anti-virus program than you are so they may be getting warnings that you are not actually seeing only your end. So this big, red, scary warning screen is what it looks like when you try to access your website when it’s been blocklisted by Google. So that’s a pretty obvious sign that something’s going wrong.
So the next most common thing that we see is spam. Spam is actually a massive problem in the website security landscape. And there’s all sorts of different kinds of spam. And I’ve seen everything under the sun. Of course the most common are knock off pharmaceuticals like Viagra and Cialis and that kind of thing, but also adult content, torrent downloads, I’ve seen Aquaponics spam, cat food, dog food, hotels, cars, one of the big ones these days is actually essay-writing services. Apparently plagiarism is a much bigger problem than it was when I was in college because there’s all these companies that will write your essays for you and they hack sites to spread their spam and their services. If Google sees any spam or relationship on your website, they’re going to issue a this site might be hacked warning and we’ll go into that in a little more detail later. But that’s going to majorly hit your SEO in a negative way.
If you can … If you want to check to see all of the links that Google is indexing on your website, just go to Google and type in site: and then your domain name and enter. Google will give you a full list of all of the links that it’s indexing on your site. And if you see some weird stuff that’s not … That shouldn’t belong there, it’s an indication that your website could have been compromised. Also if your website traffic is getting redirected elsewhere, that’s a pretty strong indicator that your website has been infected.
On the right here we see an infected HT access file which, depending on the user agent from the client is going to redirect the visitor to a spamming Russian domain. Redirects can have all sorts of different purposes. If an attacker compromises your website, they can redirect traffic to basically wherever they want. A lot of times that’s for going to spam sites, other times it will go to … Redirect to adult dating websites and in worst cases it will redirect your website to malware, ransom ware, Trojans, really bad stuff. Or a fishing page to try to steal people’s PayPal account details or their Gmail account information and that kind of stuff.
So if you or your website visitors are strangely ending up on websites they never intended to go to after they accessed your website, that’s a pretty strong indicator of compromise. Also it may not redirect all traffic. Sometimes, for example we saw a hack last year where only mobile users were getting redirected to adult dating websites. So again, it’s really important to pay attention to what your visitors are saying about the behavior of your website.
If you have weird pop-ups, weird redirects, new tabs opening up in your browser going to obviously bogus pages like the one in this screenshot here, that’s definitely suspicious. It could be caused by a misbehaving advertising network or an injected script somewhere on your website. Also we have a malware scanning service called Site Check and it’s free and anyone can scan their website for malware. So you can just head over to sitecheck.sucuri.net, type in your domain name, and it will scant the website for any known malware. We update sitecheck very frequently to make sure that it’s detecting all of the most common and the most recent attacks and payloads.
Sitecheck’s not perfect. It cannot flag things like backdoors and ATFF that don’t actually display on the website, but it’s a very useful tool to check to see if your website has any known malicious scripts loading on it. And of course if you go to your website and it looks something like this, that’s pretty self-explanatory, something has definitely gone wrong here.
All right, so now what do we do? We’ve already determined that your website is compromised. How do we actually find the infection, find the malware, and fix the hack? So I’m going to take you through a couple of steps here. What we can do is actually just use the process of elimination to go through all of the different aspects of your website. So we can go ahead and check your core files, we can check your template files, we can check your extensions, your data base, your HT access file, any third party services like Ad Networks that are loading on your website, and in some cases, the actual server itself is the problem.
And if you’re wondering, what on earth is this image on the right hand side there, it’s actually a nice juicy piece of encrypted PHP malware. So throughout the presentation, I’m going to have as many practical examples as possible because it’s one thing to talk about security, talk about malware but you have to actually know what the stuff looks like so that you can actually identify malware when you see it.
So there’s a couple of tools that you’re going to need to have under your belt here. I could do an entire webinar just on this slide, there’s so much information here, so I’m just going to quickly mention them one by one just so that you have a basic familiarity with some of the tools that we use. So the first thing, you’re definitely going to need an FTP client like Filezilla or Cyber Duck if you’re using a mac. This is so we can actually connect to the back end of your server and actually check out the files that are a part of your Joomla core and the template files and stuff.
You’re also going to want a script blocker. A script blocker is the most important security tool that you can use. What it does is it prevents malicious payloads from executing in your browser. In fact, I would recommend every single person uses a script blocker all of the time. In my opinion it’s more important than an anti-virus to use to protect yourself against hacks. You will also want to be working in a virtualized environment whenever possible because we’re assuming that your website’s compromised, right? So we don’t want your browser or your operating system, your computer getting infected to. So you can use a free tool called Virtual Box and that will basically allow you to create a sandbox environment in your laptop so that you can visit a malicious website and even if the sandbox gets infected, it’s very unlikely that that malware is going to actually jump to your operating system.
I would also recommend a browser extension called You Block Origin. We deal with a lot of cases of malware-tising and malicious ads, ad networks that have been hacked and so you’re going to want to protect yourself against those. And You Block Origin actually has a really handy diagnostic console tool that will show you all sorts of different third party scripts that are loading on your website.
We will also need to check your database. So PHP, my admin, if you’re using C-Panel or Admin-er. If you are … If you don’t have C-Panel you can just download PHP Script for database management. The database is where a lot of spam tends to go and so it’s very helpful to … We’re going to need to be able to check in there, right?
A user agent switcher isn’t a bad idea to have either because sometimes the malware is only going to execute and show on the website if a certain user agent, for example Google Bot or search engines and stuff. It’s very common for that to be the case. And so sometimes you need to actually switch your user agent in order to trigger the infection and actually see it on your end. Olsec Heads is a really good server monitoring tool. It will log any modifications to files and it’s really useful if you have a VPS of dedicated server. I would recommend having that installed and that was actually made by our very own Daniel Sid.
Support forums are another thing you’re going to want to take advantage of. The great thing about open source is that there’s a community there to help you when something goes wrong. And no matter what hack you’re dealing with, I guarantee there’s someone else that’s already had that same problem before and in the support forums, there’s a community there of people who are there to assist you and to help you.
And if you’re hosting provider supports SSH, then it’s … That’s going to make it a lot easier for you to clean your hacked site. You’re going to need some basic SSH terminal command experience but it makes it a lot easier to clean your site if you have a SSH connection.
So, before we begin please make a backup of your website first. I have lost count of the number of times I’ve seen people break their websites when they tried to remove the malware themselves. Because it can get technical and it can get quite difficult. So make a backup of your file structure, make a backup of your database, and make sure to store these backups in a secure location. I’ve seen a lot of times people store their websites on like the public placing directory of their production servers and that’s a really big security risk. So before you make any modifications to your site at all, please make a backup so if something goes wrong you can revert back to it and start again.
So let’s get to the good stuff. First thing you’re going to want to check is the Joomla core files. The modification of Joomla core files is probably the most common thing we see in terms of where the malware’s actually located. We have to remember that the goal of the attackers is to spread malware to as many people, as many website [inaudible 00:13:35] they can and the core files is a really good way to do that.
In the example image here, this is actually a hacked index.php file and it is … We can see the code at the bottom of the file is actually legitimate and the code at the top is actually injecting spam into the website. So you’re going to want to check the integrity of your core files. And there’s a number of ways you can do that but one easy way is to download a fresh copy of whatever version of Joomla that you’re using and compare the website files to the ones that are on your server. If you have an SSH connection to your website, then you can do that directly on your server. If you don’t, than you can actually download your website to your local machine and you can compare the files that way.
Now I’m not talking about comparing them one by one by one, that would take a small eternity of course. But there are some … I’ll show you in the following slides of how you can actually figure out which files are the hacked ones. So if you’re really not sure, what you can do is you can download a copy of the same version of Joomla that you’re using and using the FTP client, just replace all of the core files on the server and that will remove any malicious modifications that have been made to them.
This is the default.php file of Joomla. This is a clean file, there’s no malware here and the index.php file is very commonly infected but we can also see, if you look near close to the bottom, there are two files being called directly, the defined and the framework.php files in the includes directory. And as such, since they’re called directly from the index.php file, this is a really common place to store malware. And I’ll show you a couple examples.
Here is a hacked defines.php file. We can see at the top and at the bottom of the file, that’s all legitimate, that’s all what it’s supposed to look like. And there’s this big, ugly, encrypted chunk in the middle which is the malware. So if you see a file like on this on your Joomla website, just delete the encrypted chunk there in the middle or replace it with a stock clean file.
Here is an even more ugly framework.php file. So a lot of the time, as we can see here, a lot of the malware is encrypted in order to kind of obfuscate what the infection’s actually doing. And I’ll bring your attention to the very top of this file. We can see that there’s an opening php tag at the very top left and there’s a big chunk of empty space afterwards, before the malware actually loads. This malicious code is actually one line. It’s all just one big chunk. But what the attacker has done is they’ve placed the malware way off to the side so if you were just to open up the file in a regular text-editor it would look normal until you scrolled, scrolled, scrolled, scrolled all the way to the right of the file.
This is a really common way to hide what they’re doing. So if you’re using your text-editor, make sure that word wrapping is enabled like in this image here so that if it’s not … If it’s displayed off the screen, it will bring it back to … So it’s visible, so you can actually see it. Now it’s also really common with malware for them to place the malware at the very top of a file because that ensures that the malicious code loads before everything else does and it ensures that the payload is delivered.
The thing about Joomla is that, unlike some other CMS’s there’s three different branches of development with Joomla. There’s 1.x, 2.x, and 3.x. 3.x is the most recent version and it’s currently in active development. 1.x and 2.x are no longer getting patches, they’re no longer in active development and we see a lot of people that are stuck in these old versions of Joomla because … And they’re unable to update to the most recent version. And this is a really big problem, specifically as it relates to Joomla. Because some people using 1.5.26 or some other old, out of date version, they may not have the technical expertise or know-how to update to the most recent version, they may not have the resources or the money to hire a developer to do it for them, and they may not understand why it’s such a big risk.
So if any of you watching are using an old version of Joomla, I would recommend that you get a game-plan to upgrade … Migrate to 3.x as soon as you’re able to. This should be your first priority from a security standpoint. And I you’re absolutely stuck in 1.x or 2.x, there are other options and I’ll go through those at the end of the presentation.
So if you want some guidance on how to migrate your site to the most recent version, these are some good resources to go through from the official Joomla documentation and you can go there and it will walk you through step by step. And unfortunately it’s not a one-click operation, you do have to follow some procedures, but there is documentation out there to help you.
How do you actually tell which files are bad? Joomla has a lot of files and as I mentioned, going through each of them one by one would take forever. So there are some things that we can do to actually determine where the differences lie. So in this example here, I’ve downloaded the website files onto my local computer and I have a fresh copy of Joomla next to it of the same version of the example.com. And using this dif command, difexample.com and then the Joomla directory, it’ll spit out the differences between the two.
So for example we see there are some files that only exist in example.com at the top, that bogus zip file and a couple of php scripts that aren’t supposed to be there and we can also see in the middle of the image example that there are some differences between the index.php file and it basically just prints out the difference between the two and we can see there’s some stuff about Google Bot and it’s a spam infection, basically.
If you want to check to see which files have been recently modified on your server, you can use this command. You’ll need an SSH connection to the server in order to deploy this. But basically this command will tell you which files have been modified within the last 15 days. Now sometimes you’re going to have to go further back than two weeks because what’s pretty common is for attackers to place a backdoor on the website and then just wait for a month before they actually execute their payload. The reason they do this is because the first thing people do when they’ve been hacked is to revert to a recent backup. But if the backup itself is infected, then the attacker is just going to reinfect the site with the backdoor, right?
Now I should mention, don’t freak out over any and every modified file. If you’ve updated your templates or updated Joomla, updated your extensions, these are going to be recently modified files too so just because it’s recently modified doesn’t mean it’s bad. But it’s definitely suspicious and it needs to be investigated.
So next is the template files. This is also an extremely common place for attackers to place malware. We can see in this image here that all these files have not been modified since 2010 except the index.php file which is super suspicious, right? And it’s almost … In Joomla, in terms of the template files, it’s almost always the index.php file so that one you’re going to want to look out for in particular. You can download a fresh copy of whatever template that you’re using, make sure it’s the same version, and overwrite the files using your FTP client. Now if you have made any customizations or any modifications to your template files, those changes will be reverted also so that’s why it’s so important to make a backup before we begin cleaning the site, right?
Make sure that you’re always obtaining your templates from a legitimate source. Make sure it’s either from the official repository or if you’re buying a premium template or something like that, make sure you’re not just downloading a hacked version of it because they always contain malware.
Here’s an example of an infected index.php file in Joomla template. That big chunk of script in the middle is the bad stuff. And this is called bogus J query malware and it’s one of the most common infections that we see with Joomla websites today. We can also see in this image that there’s a bogus file that’s been placed in the java script directory called stats6ba.php and any php file located in a java script directory is usually bad.
So if you’re website is infected with bogus J query, sitecheck will detect it and it will look something like this. So you’re also going to want to be careful with your extensions, right? You want to check … Sometimes, it’s not as common in Joomla for this to be the case, but sometimes extensions themselves are hacked and are the source of the infection. So you can … Say for example you’re seeing spam load on your website or it’s getting redirected, you can go to your Joomla administrator panel and disable all of your extensions and then see if the problems still exist. If the problem goes away, then it’s one of the extensions and you can go through them one by one by one to see what the issue is.
More commonly with Joomla though, the issue with the extension files is that they’ve had backdoors placed in them and you know, there are a lot of files to go through so this is why it’s important to use the commands I showed earlier about checking for recently modified files. Again, same thing with templates, you want to make sure that this … Your plug-ins and extensions are coming from a legitimate source, don’t use hacked software and if you’re really just not sure what to do, you can download fresh copies of all of your extensions and just rewrite them, overwrite them on the server.
So here’s an example of a backdoor that’s been injected into a plug-in file in Joomla. Again, very heavily obfuscated, very difficult to see what it’s actually doing, but it is a backdoor.
All right, we’re also going to want to check your database, particularly if you’re seeing some spam load there. So if you’ve searched up your website in google and you see a bunch of Viagra spam or whatever, you can hop into your database and just perform a search for Viagra and see if you can find where the spam is located and then you can delete it from there.
Database spam infections can be really difficult to clean. They are very time consuming because often they’ve injected thousands of lists into your website. And for Joomla, it’s most commonly in the jos_content table. That’s where all the content of your posts and stuff and articles are located. Sometimes attacker will inject links into existing articles that you have on your website and other times if they’ve been able to access your administrative panel, they’ll actually just post a whole bunch of completely bogus articles.
Now this is going to be a big hit to your SEO because once Google sees this kind of stuff on your website, you’re all of a sudden associated with these spamming domains and your SEO is going to take a hit and it can take awhile to get back into Google’s good books there. We can see at the top right of this code, that it says display none and that does exactly what it sounds, it makes sure it doesn’t display. But the code is still there. So your visitors and yourself when you’re visiting your website, the site will behave normally, everything will look fine, but when Google combs your website, it sees all this spam, right?
The next step that we’re going to check for is your HT access file. On the right, this is what the default, clean Joomla access file should look like. If you are getting redirected on your website to spam sites or exploit landing pages or something like that, the HT access file is going to be one of the first things you’re going to want to check. Sometimes the attackers will place the HT access roles way, way, way at the bottom of the file so you have to scroll down before you can actually see it. But if your HT access file has been modified recently, you’re definitely going to want to check the code inside to see what’s in there.
So this is an example of a hacked Joomla HT access file. Again, a spam infection, very common, we can see it’s checking for different search engines and if it’s not a search engine then it doesn’t execute. If it is a search engine, then it will display the spam. So we can see it’s referencing index.php which has been modified and it’s also referencing main.php which is totally bogus file that doesn’t belong in Joomla anywhere.
Now advertising networks are something that we’re going to want to check too. Not just ad networks, but also any third party content that you’re loading on your website. You should treat the integration of third party scripts on your website with caution. Because it’s a server that someone else owns that you can’t ensure the security of. We’ve seen cases of mal-vertising where hacked ad networks or bogus ads have distributed Trojans or sometimes even worse ransom ware. So if you do … If you are getting weird redirects and strange behavior on your website, try just disabling your ad networks all together and see if the problem goes away. And from there you can maybe consider using a different networker or a different service as a replacement.
We see this issue a lot on like video streaming websites that are using four or five different ad networks and it can be very difficult to trouble shoot which is the actual culprit. So I would recommend, if you are going to use an ad network on your website, I would recommend that you stick with the reputable ones like Google AdWords and whatnot.
So this is an example of a bogus ad network injection in a database in the jos content table. So basically these scripts were located at the bottom of all their articles and anytime a visitor to the website clicked on any links or clicked … Even just clicked on the background, a new tab would open up and redirect the user to guess what, a spam website.
And in some cases it’s actually the server itself. This is not as common but it does happen. But server operating systems can become infected with rootkits just like any other operating system, right? So if this … If you’re unfortunate enough to have this happen to you, the best thing to do is to migrate your site to a brand new server and just have that server completely reformatted. You can clean a rootkit from a server, but the best practice is to reinstall the operating system so you can be absolutely certain that the problem is gone.
You will want to speak with your hosting provider about security. It’s never too early to have that conversation, right? Different hosts have different procedures in terms of what they’re going to do if your website gets hacked. Some hosting providers will clean the hack for you, others will disable your website until you, yourself clean it, and some hosts don’t really do anything at all. So it’s an important conversation to have and something that you should be wary of, right?
And just to reiterate, Olsec Heads is a really awesome tool for monitoring your virtual, private server over your dedicated server and it’s one of the best tools that you can have in your arsenal, for sure.
Now the hardest part is finding and removing all of the backdoors. Sometimes attackers will just leave one or two backdoors on the server, sometimes they’ll put a backdoor in every single php file that they have access to. Sometimes they can be really aggressive. Backdoors can be tricky to find, too. Because there’s new ones being written every day, there’s no one single backdoor that you can look for. But they do have some consistency between them. Often they’re lodged at the very top of files and other times … You’re going to want to check to see if there’s any recently modified files on the server. Often those are backdoors. If you have access to your server logs, then you can check to see if there’s any particular files that are getting directly accessed by strange IP addresses in countries that normally wouldn’t have any business accessing your website. And if you’ve got an SSH connection to your website or if you’ve downloaded your file to your local machine, you can search the file content using the grep command for these sorts of php functions which are very, very frequently used by backdoors.
Now remember, just because a file has a val bay 64 in it, doesn’t necessarily mean it’s bad but it does definitely warrant further investigation if you see any of these sorts of things being used.
Here’s an example of a backdoor launched at the bottom of the Joomla file. The code a the top is legitimate, it belongs there. And the attacker has placed a backdoor at the bottom of the file to maintain access to the website, even if you’ve removed the payload, they’ll reinfect it, right?
So there’s some more resources that you should be aware of. Sitecheck, as I’ve mentioned before will scan your website for malware. Unmask Parasites made by our very own Dennis is great for checking for spam, malware, and that sort of thing. Redleg File Viewer at awsnap.info is very useful again for checking for spam. Webpagetest.org is useful because it’ll load your website and it’ll tell you every single file, every single script that’s loading and so it’s a very good diagnostic tool. If you want to go fully down the rabbit hole, you can download the Burp Suite which is a web application testing tool. And if you find some interesting encrypted php code on … Within your site files, you can use DV Code or Unphp.net to see if you can decrypt it to see what the code is actually doing.
All right, we fixed the hack, now what do we do? A lot of people do nothing and just hope the problem goes away but the fact of the matter is, once the attackers find a website that’s easily exploitable, they’re going to do it again and again and again and again because they know that most people don’t change they’re passwords, most people don’t update their websites and keep them well maintenanced, so they will keep coming back again and again until you take some proactive steps to prevent them from doing that.
So the first thing that you’re going to want to do is update all of your software. Update Joomla, update your template files, update your extensions, and this is … There will be no point at which your website is fully patched forever because what is considered safe today could be considered vulnerable tomorrow, right? So this is a constant process, just general everyday website maintenance is the best line of defense you have against attackers.
You’re going to want to change all your passwords too and make sure that you’re using strong, difficult to guess, difficult to brute force passwords. This is one of the leading causes of infection next to out of date software. And once your website has been compromised, it’s best to just assume all of your passwords are compromised so change your Joomla admin panel passwords, change FTP passwords, change your C-Panel password, change your database password, just change them all just to be on the safe side.
You’re also going to want to review who has access to your website. How many admin users do you have in Joomla? How many FTP accounts do you have? Who has access to them? Why do they have access to them? For how long do they have access to them? How long do they need access to them for? It’s best to have as few admin users as absolutely necessary, as few FTP accounts … Basically the fewer software and whatnot that you have on … And users, the less chance there is of something going wrong, right?
For example, here is a malicious super administrator in the Joomla dashboard. These ones are usually pretty easy to spot because they have suspiciously generic names, in this case, service Joomla user helper and so you’re going to want to make sure if the attackers have placed any malicious accounts on your website to remove them. Sometimes I’ve seen websites where a website owner has hired a developer to work on their site for sometime and they created an admin account for them and then they never removed it when the developer was done working on it and that is sometimes … Even years down the road, the reason why the website gets hacked because that accounts gets compromised.
You’re also going to want to do what we call in security world, decreasing the attack surface. So again, the fewer extensions you have, the better. If you have any old templates on your website that you’re not using anymore, remove them. Remove any unused plug-ins, modules, components. If you have backups of your website laying on your production server, migrate them off, remove them. If you have any development versions of your site on your production server, remove them. Just, basically the fewer software … The less software, the better, gith? And the less chance of something going wrong, in that case.
This is also sort of the least privilege, you know. Just make sure … Have the least amount of stuff so there’s less things that the attackers can possibly exploit, right?
You’re also going to want to check your laptop and whatever work station that you use to connect to your website. I’ve seen clients that have updated all their software and changed all their passwords and they got hacked again the next day because there was a malicious Trojan key-logger on their computer and the attackers were able to just get the new password and reinfect their site immediately. I would caution you against administrating your site from public wifi networks. If you are going to do that, I would recommend that you will … I would always recommend that you use encryption, use SFTP or SSH rather than FTP.
And you’re also going to want to make sure that you have regular backups of your website. This is often overlooked but it’s so important because it’s your best tool on a rainy day. If you’re able to just revert your website back to a known clean state, then you can just change your passwords and you’re good to go.
Again, need to reiterate, don’t store your website backups on your live server. We do have a backup service as well, it’s $5 per site per month and this is an example of the dashboard that’s in use there so you can just grab a previous version of your website from … Whenever you need and deploy it onto your server and you’re good to go.
You can also do some hardening on your website. Any default settings for any software are considered to be not-optimum. So you can do .. This is an example of a HT access file that’s basically prevents php from being executed in whatever directory in which it resides. So you can put a file like this in an images … In your images directories or includes directories, places where php just doesn’t need to be executed. It’s really common for attackers to exploit vulnerable image uploading software and so if they’re able to upload a backdoor into an images directory, they won’t be able to exploit it.
And you’re also going to want to use a security plug-in. I would caution you against installing every single security plug-in under the sun. Sometimes these plug-ins will be doing similar things and I’ve seen people get locked out of their admin panels because of too much security software. So pick one, maybe two and stick with those.
And you’re also going to want to make sure that logging is functional. Test to make sure that the plug-ins are actually sending you email alerts when something goes wrong.
And last but not least, use a web application firewall. This is … I can’t recommend this enough. We do offer one called Cloud Proxy. This is particularly useful if you’re stuck using an old version of Joomla. Basically it will virtually patch and protect your website and filter out any malicious traffic and it will prevent your website from DoS attacks. I would recommend every website owner use a website firewall. Everyday websites get attacked all the time and if you’re behind Cloud Proxy or some other web application firewall, then the chances of you getting attacked or hacked is way, way, way less. And it’s also a fully global content distribution network and so it will speed up your website performance as well.
See Full Transcript
ExpandIn the website security community, our name is known for fast site hack cleanup and responsible vulnerability disclosure. As thought leaders in website security, we are committed to sharing what we know. Follow our concise and helpful website security guides and tutorials so you can learn how to clean and secure your website.

Join us on April 5th as we cover the latest findings from our 2022 Hacked Website Threat Report. We’ll shed light on some of the most common tactics and techniques we saw within compromised website environments.

All software has bugs – but some bugs can lead to serious security vulnerabilities that can impact your website and traffic. In this webinar, we dive into the steps you can take to migrate risk from infection and virtually patch known vulnerabilities in your website’s environment.

The threat landscape is constantly shifting. As attackers continue to hone their tools and exploit new vulnerabilities, our team works diligently to identify and analyze threats posed to webmasters. Join us on July 6th as we cover the latest findings from our Hacked Website Threat Report for 2021.

In this webinar we will highlight the various activity, access, and error logs WordPress site administrators have at their fingertips. Plus, learn how logs can best be used to manage, troubleshoot, and most importantly, secure your sites.

In our latest webinar, we'll describe action items that can improve the security state of internet-connected devices we all use every day. These devices will include common household staples such as: WiFi Routers, iOS/Android devices, and personal computers.

Join us as we delve into the minds of hackers to explain targeted attacks, random attack, and SEO attacks. Find out why bad actors target websites.
A feature benefit guide for our agencies and end users. Why use our firewall? What kind of protection does it offer? How does it affect the efficiency and speed of my site? Will it affect my server's resources? Find out the answers to these questions and more in our webinar…..

Cross-site contamination happens when one hacked site infects other sites on a shared server. This webinar is for beginners and web professionals to understand cross-site contamination and how to prevent it…..

If you're considering security for your site or are new to our services, this webinar will guide you through Sucuri's simple setup processes. Potential notifications, support options for various scenarios, and ways that you can also work to keep your site malware-free will be discussed…..

Learn how you or your agency can account for security with your client projects. Presented by Sucuri Co-Founder, Dre Armeda, this webinar shows how you can get involved and help clients who are not aware of some of the security risks involved with managing a website…..